Murphy’s Law Comes to DevOps: Is Security Wreaking Havoc?
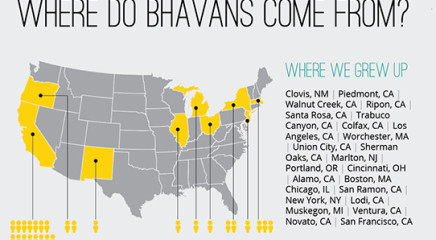
(Editor’s note: Joe Franscella, a vice president managing several category-leading client accounts at Bhava, is also our resident security and DevOps enthusiast. Below are his key takeaways from the debut posting of his new column at DevOps.com where he’ll entertain and answer some of the biggest questions in this brave new world where security is forced to meet continuous software development. We’re excited to follow his insights in the coming months.)
DevOpsSec… Rugged DevOps… DevSecOps… Am I missing any?
It seems like the only thing more bountiful than the volume of terms popping up to describe the different facets of how security supports DevOps is the number of vendors selling products and services purporting to “solve” all these security-related problems.
To be sure, we’ve seen some compelling offerings crop up and it’s likely a good number of them do accomplish the job they claim to. Regardless of whether that “job” is actually something that needs to be done to solve a DevOps-related security issue, that in itself is a job for professionals in the developer, operations and security communities to sort out. And, hopefully, a topic they’ll be interested in discussing here.
The new DevOps.com column’s point is to go looking for problems and solutions. Specifically, it’s focused on how and if DevOps is causing things to go wrong in security (and from time to time in other spots) and what DevOps-focused organizations are doing to correct course.
Some Security Questions to Ponder in Future Columns
- Is it true that security can’t keep pace with “continuous?”
- Will “agile” and security always be oil and water?
- Will DevOps and security never achieve a harmonious “peanut butter and chocolate”-like relationship?
- Or, is the talk about how DevOps is the best thing that has ever happened to security and a great opportunity, actually the new reality?
Another great question this column seeks to answer is whether any of the so-called security problems DevOps is creating are anything new, or if they are the same old challenges that have existed since the first bit of sensitive data was exposed to the Internet decades ago.
There are times when I may mention specific vendor solutions in this column, but only if an actual end user or practitioner is attached to the reference. If that happens, I will always point out if any are clients of mine at my day job.
It’s no coincidence that the DevOps.com column is being launched alongside RSA 2016, as DevOps Connect: Rugged DevOps @ RSA Conference is a major part of the big show, and, that is where the world will be talking DevOps and security after all. Here’s hoping the event will expose problems and provide solutions.